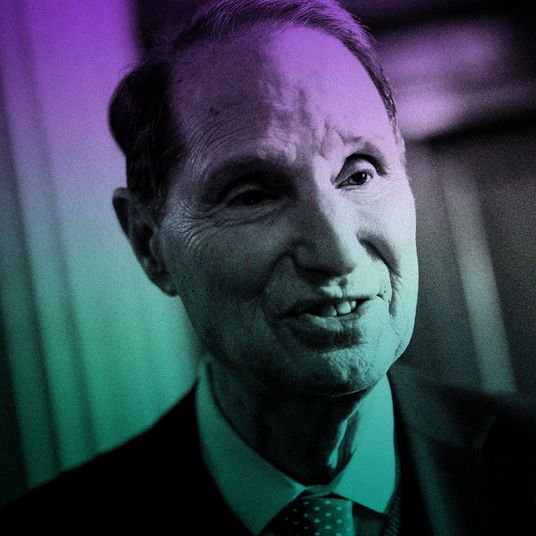
Before last month, only the biggest geeks working in corporate IT departments and law-enforcement agencies had ever heard of Mandiant, an Alexandria, Virginia–based cybersecurity firm that helps companies identify and respond to security breaches on their computer networks.
That all changed when the New York Times began a series on Chinese computer hackers, first detailing attacks on its own servers and naming Mandiant as the firm it hired to repel them, and then publishing details of Mandiant’s report that linked a wave of U.S. corporate hacks to a People’s Liberation Army cyberespionage division called Unit 61398.
But as Mandiant cements its reputation as a cybersecurity media darling, it is also drawing attacks from rivals, some of whom see it as a Johnny-come-lately that is simply popularizing the work done by other firms.
“They’re certainly the biggest out there, and they’ve been doing it for a number of years, but they’re not the only ones,” says Dmitri Alperovitch, of cybersecurity firm CrowdStrike, one of Mandiant’s main competitors. Alperovitch highlighted some of the same Chinese hacking activity identified by Mandiant, which he connected to a malware program called Shady RAT, in a 2011 paper.
In an interview with Daily Intelligencer on Thursday, Mandiant CEO Kevin Mandia defended his firm’s timing, saying, “Mandiant’s not the first company to blame China for the hacks, but it was our turn to carry the ball for a little bit.”
The world of corporate cyberdefense is a close-knit circle of security experts, many of whom know each other from stints in the military and law-enforcement agencies. Few were willing to call Mandiant’s success undeserved, and many acknowledged that it had done good work in promoting its findings. But some said that while Mandiant is one of the best-known firms that works with major corporations, its prominence isn’t always reflective of better work.
Specifically, some rivals point to weaknesses in Mandiant’s recent report, which traced the hacking activity that compromised data at the Times and other major corporations to Unit 61398, a building on the outskirts of Shanghai that is thought to contain a major military hacking operation. Jeffrey Carr, the CEO of Taia Global, publicly attacked the report, accusing it of having “critical analytic flaws,” including leaving out other major sources of international hacking, like Russia. Other competitors acknowledge that while Mandiant was the first company to corral major evidence that the People’s Liberation Army of China was behind some of the high-profile U.S. hacks, it was far from the final word on the subject.
Chester Wisniewski, a senior security adviser at Sophos, says that Mandiant’s Chinese hacking report is “impressive in length and girth, but not any other way. There’s nothing groundbreaking in there.” Alperovitch concurs. “The report itself didn’t highlight any new hacking activity. They did a nice job with attributing it to the P.L.A., but the story’s been beaten to a pulp.”
Some of the backlash against Mandiant is surely attributable to jealousy. But more serious lines of criticism have emerged — namely, that Mandiant’s report was too quick to tie an international hacking scheme to the Chinese military, inflaming diplomatic tensions without concrete evidence of the military’s involvement. Mandia allows that his firm’s research couldn’t definitively conclude that the P.L.A. was behind the hacks, but he says that making the data public was an unimpeachable public good.
“What do they want us to do? Get into the third floor of the [Unit 61398] building and start interviewing people?” he says. “We’ve done the best we can do with the data we have.” In Mandia’s view, releasing a not-quite-conclusive report was better than doing nothing. “You could feel that in the last month, the frustration was building in the private sector,” he says. “It came time to say, ‘Let’s get the data out there, the IP addresses, the malware they use. Let’s get it into the government’s hands. Let’s give these guys a Mike Tyson uppercut.’”
Mandia is adamant that his company’s work is not politically motivated, and that he has no particular grudge against China. Still, many foreign-policy experts expect a robust response from the Obama administration in the near future over the issue of cyberespionage (which was singled out for attention in the State of the Union Address earlier this month), with a specific focus on the role China has played in international hacking efforts. If that happens, the work done by Mandiant will no doubt play a large role in negotiations.
“We all know it’s the Chinese most of the time in this industry, but most of us aren’t willing to stand up in front of the public and say, ‘It’s the P.L.A.!’” Wisniewski of rival firm Sophos says. “It’s brave of them to come forward.”
For the last few weeks, Mandiant’s offices in Alexandria have been quietly bustling. There have been no parties or celebrations, no Champagne toasts to the Times, but business has been good. The company got a fawning profile in Bloomberg Businessweek — which called it “the 800-pound gorilla” of anti-espionage response firms — and Mandia was booked on many major TV-news networks. Such a sudden rise to prominence has caught the modest CEO off guard.
“It’s very rare,” Mandia says. “I’ve responded to requests for fifteen years, and they rarely make the front page.” Mandia maintains that he never courted so much attention. “We aren’t media mongers. We spent nine years in business, handling problems discreetly. I’m a little surprised by all the press, honestly.”
Of course, a rising tide lifts all boats, and Mandiant is not the only firm to benefit from the popularization of the Chinese hacking scandal. Most of the security firms contacted by Daily Intelligencer reported an influx of new client requests since the original Times story ran.
“Across the board, we’ve seen a lot more media interactions and people interested in helping them find out if they had similar activity in their systems,” says Rocky DeStefano, founder of security firm VisibleRisk.
Partly because they also stand poised to gain new work as the result of Mandiant’s success, some rival firms are biting their tongues and acknowledging that while Mandiant’s report may not have been perfect, they’re glad the issue of cyberespionage is getting the attention it deserves.
“This is not sour grapes — they did a nice report and came out with new information,” Alperovitch of CrowdStrike says of Mandiant’s recent efforts. “It’s their turn now. They should enjoy it.”