The current public dispute between Apple and the FBI concerning San Bernardino shooter Syed Rizwan Farook’s iPhone is complicated and messy, full of technical details, software intricacies, and big (and scary) gaps in knowledge about the hardware details and engineering capabilities of the government and Apple. It’s also extremely important. If you want to follow this case without drowning in jargon, here’s a glossary you can reference whenever you’d like to sound smart.
Apple
A computer company based in California. Apple makes the iPhone hardware and the operating system that powers it. Last week, Apple was ordered by a federal judge to create a software package disabling some of the iPhone’s built-in security features and to help the FBI load it onto an iPhone owned by Syed Rizwan Farook, one of the San Bernardino shooters. Apple refused, and its CEO, Tim Cook, authored an open letter objecting to the order.
Usage: I just purchased a new iPhone from Apple.
backdoor
An unpublicized and covert vulnerability in software that can be exploited for surveillance or intelligence-gathering purposes. Essentially what it sounds like: a secret method of getting access to a system.
Intelligence agencies like the NSA have tried to push tech companies to build backdoors into their systems for the government to use whenever it deems necessary. Every major tech company has denied being complicit in building backdoors into their systems.
Usage: Hello, hacker friends, I found a backdoor in the latest software update that lets us steal info from users.
backup
iCloud, Apple’s cloud service, automatically backs up phone data. But it only creates automatic backups when the device is connected to a trusted Wi-Fi network and charging. As part of its investigation, the FBI had the password on Farook’s account reset, disabling the auto-backups.
If the automatic iCloud backups had continued, the phone’s data would be accessible to the FBI on Apple’s iCloud servers — and the FBI wouldn’t need to access the phone itself, and the judge wouldn’t have issued the order to Apple.
Usage: There are a lot of important drawings of Sonic and Tails kissing on my phone, so it’s set to create a backup automatically.
brute-force attack
A crude intrusion tactic that relies on, well, brute force. Let’s say you’re trying to guess a 4-digit passcode. If you know the device’s owner, you might try entering their birthday (which is definitely not my passcode). Or maybe a lucky number, or their wedding date. A brute-force attack wouldn’t even try to intuit those details; it would start at 0000 and iterate one by one up to 9999.
A brute-force attack is one that tries every option. It’s not efficient and aside from the simplest passwords, would take years to complete. An iPhone can process an unlock code every 80 milliseconds. A four-digit passcode would take 13 minutes to crack; a six-digit one would take 22.2 hours. According to Apple’s latest security whitepaper, “it would take more than 5½ years to try all combinations of a six-character alphanumeric passcode with lowercase letters and numbers.”
Usage: Karen uses the same PIN every time, so we don’t need to brute-force attack to gain access to her account.
cloud
In this case, “cloud” is short for “cloud computing.” The cloud refers to computer operations that are handled remotely — on big server farms somewhere else in the world, and not locally, on your phone or computer. Many of your mobile device’s functions, such as email or Siri, are executed remotely via the cloud. When a file is stored “in the cloud,” it’s stored on a disk that is linked to the computer via the internet, as opposed to local storage, which refers to the hard drive in a computer. A central component of the current dispute is that Farook’s iPhone’s data is not accessible via the cloud — it’s only stored locally.
Usage: All of my family photos are in the cloud so I can access them on any device.
Device Firmware Upgrade Mode
An iPhone mode in which iOS doesn’t load, but the phone can still interact with software (like iTunes). Putting a phone into this mode is how jail breakers (people who install custom software on iOS) get around certain restrictions; it’s what the FBI would activate to install the Software Image File that it is directing Apple to craft.
Usage: Hey, reboot the phone into Device Firmware Upgrade mode so I can install this sweet new custom iPhone software.
encryption
A system of protecting data and information stored on a computer. Encrypted data is basically unreadable unless it is “unlocked” by an encryption key. Without the right passcode to unlock the iPhone, the files on it remain encrypted and unreadable to the FBI.
Usage: I encrypt all of my My Little Pony: Friendship Is Magic fanfic because there are spies everywhere.
Federal Bureau of Investigation
The government agency hoping to gain access to the iPhone in question, which belonged to one of the San Bernardino shooters.
Usage: [at a bar] I work for the FBI, which stands for Federal Bureau of Investigation.
firmware
Base-level software that powers most computer technology. On an iPhone, the firmware is what runs before the operating system boots up. Because it runs at the lower levels of a computer, firmware vulnerabilities allow deeper levels of intrusion, are more difficult to detect, and don’t disappear if, say, a device’s OS is wiped completely. In this case, the FBI is asking for custom firmware that will disable the security delays that deter brute-force attacks, allowing them to enter passcode guesses as fast as the hardware will allow.
Usage: I just installed a new firmware upgrade for my router, which patches a security vulnerability. Wait, why are you leaving?
iCloud
A suite of “cloud” services offered by Apple which ties into iOS and its other operating system, Mac OS X. iCloud offers, among other features, remote file storage and syncing between devices, as well as automatic backups of mobile devices.
Usage: I love to sync my files across devices with iCloud.
passcode
The code required to unlock and access information stored on the iPhone. Standard iOS passcodes used to be four digits, but the default was upped to six digits on iOS 9. Users can make their passwords more complex if they’d like, using alphanumeric characters as well as punctuation symbols.
On the iPhone in question, iOS 9 introduces time delays between incorrect passcode entries. The device is wiped after the tenth incorrect entry. That makes it impossible for the FBI to try to brute-force the passcode in its current state.
Usage: My passcode is absolutely not my birthday, so don’t even try it. Seriously. That’s not it.
Secure Enclave
A processor in newer iPhone models that’s completely separate from the rest of the device. It handles all cryptographic operations on the iPhones and enforces security measures like the passcode delays and wiping the device after ten failed attempts; it also processes fingerprint authentication for Touch ID. Because it’s separate from the rest of the device, it’s theoretically more secure.
The iPhone 5c owned by the San Bernardino shooter does not have a Secure Enclave. But because it’s a key feature of other Apple products that the FBI might be interested in, security experts are concerned: If a precedent is set that Apple must comply with the current order, what’s to stop them from also being ordered to create software that alters the Secure Enclave? (This sets aside the still-open question of whether it’d be possible to alter the secure enclave.)
Usage: Even if we rebooted the iPhone, passcode delays would not be reset because they are handled separately, by the Secure Enclave.
signing keys
In order to upgrade software or firmware on an iPhone, the device needs to ensure that the upgrade is legitimate. Signing keys are authentication files that Apple uses to confirm the origins of its software upgrades. Software like the type the FBI wants needs to include Apple’s signing key in order to be installed on the device. If Apple were ordered to turn over their signing keys, the FBI would be able to install its own software on any iOS device. The FBI is not currently requesting these and it’s highly unlikely but not impossible that Apple would be forced to hand them over.
Usage: [Extremely big government voice] Now that we have Apple’s signing keys, we can loaded secret spying software onto any device we want.
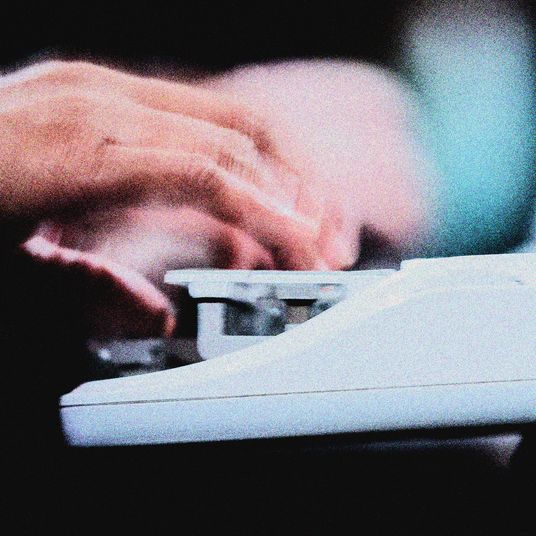
Software Image File
The piece of software that the FBI is directing Apple to build. They want software that will disable the time delays between passcode inputs, allowing them to enter each one as fast as possible, every 80 milliseconds. Given that it could take up to five and a half years to crack a six-character alphanumeric code, one could intuit that the FBI is probably working on a more simple four- or six-digit code. Some are referring to it, cutely, as FBiOS.
Usage: Hey, Tim, FBI here. Can you make us a custom Software Image File for this iPhone?