You’re an American citizen, returning from a trip abroad. As you pass through customs, what can customs agents do with your phone, laptop, tablet, or any other digital device you may be carrying? As U.S.-born NASA scientist Sidd Bikkannavar found out when returning from Chile in early February, they can aggressively press you to give up your phone’s PIN, copy everything on your phone, and then send you on your way.
While the U.S. Customs and Border Protection (CBP) is the nation’s largest law-enforcement agency, it operates under a significantly different set of regulations than your local police department. And that means it can search the phone of anyone — whether you’re a U.S. citizen or foreign national — who crosses the U.S. border, even without the suspicion that someone is committing a crime.
Why? It all comes down to something called the “border search exception.”
The Fourth Amendment, the border, and you
As a citizen of the United States, you’re generally under the protection of the Fourth Amendment, which protects against the search and seizure of your person and belongings without law enforcement first finding probable cause, and obtaining a warrant from the courts.
But the Supreme Court has repeatedly upheld that the Fourth Amendment’s requirements that law-enforcement agents produce probable cause and obtain a warrant are suspended at the border, due to the public interest in preventing the entry of dangerous weapons, drugs, or illegal content like child pornography.
This exception has been in place for decades, but has only recently become a larger privacy concern. Before the advent of laptops and smartphones, “the privacy interest was relatively low when you had one piece of luggage for a week-long trip to Baja,” says Sophia Cope, staff attorney for the Electronic Frontier Foundation. Even if you were carrying your work briefcase, there was a hard limit on how much information you could carry — there’s only so much paper you could fit in there. Not so much when your phone or laptop could contain everything from personal photos to tax records.
In August of 2009, CBP Directive 3340-049 laid out its policies on searching electronic devices (it’s explained in a-bit-more-understandable English in the CBP’s Privacy Impact Assessment). While it had already been searching electronic devices before this, the CBP’s directive formally declared its position, which is clear cut: “In the course of a border search, with or without individualized suspicion, an Officer may examine electronic devices and may review and analyze the information encountered at the border.”
In other words, CBP agents can take a look at your phone whenever they feel like it. “DHS’s official position is they do not need any level of suspicion in order to search a person’s mobile computing device, whether a laptop or a cell phone,” says Greg Nojeim, senior counsel for the Center for Democracy and Technology.
Your options
If, for whatever reason, you don’t want to have border agents sifting through your personal data, you have a few options when traveling.
You always have the right to remain silent — and this extends to not revealing your password or PIN when asked. “Some courts have found that a person cannot be compelled by the government to disclose their password, because it can violate their right against self-incrimination,” says Nojeim. This protection, however, may not extend to any device that can be unlocked with your fingerprint or other biometric indicators.
The distinction is a subtle but important one: Your PIN or password is information you have memorized in your mind, which courts have repeatedly affirmed you cannot be forced into giving up. Your body, however, is not so free — so federal agents can force you to unlock your phone using your fingerprint. You may want to disable that fingerprint-unlock feature on your phone before you travel.
Regardless, clamming up about your password can only take you so far. If the CBP is determined to see what information you have, they can detain your devices until a legal search can be completed on them. This means, while you will eventually be allowed to reenter the U.S., your device will stay behind. If they want to do a deeper dive on your device, they need only have “reasonable suspicion” — a looser standard than probable cause, and one that doesn’t require a court’s approval — to use various tools on your devices in an attempt to unlock and do a deep search of your data.
The safest (and most expensive) option is to travel with a separate phone or laptop altogether. Before heading to the airport, wipe your travel phone and laptop (after backing up vital data to a cloud service somewhere). When returning to the U.S., you can present your phone and laptop if asked — without worry.
If that’s not possible, you can also turn to full-disk encryption to protect your information. (The iPhone uses encryption by default, and there are numerous solutions for doing the same to your Mac or PC laptop, as well as an Android device.) The issue here is that you’ll still be asked to power on your device and provide your password, meaning any encryption you had in place on your phone or laptop will be rendered useless. If you choose to not give up your password, your device can still be detained, and forensic tools used to attempt to decrypt it, if the CBP has reasonable suspicion.
And finally, if you are pulled aside for further screening, you can choose to simply give up your password and hope you can make it through without losing your device, or without being detained for a significant period of time. You may still want to take a moment before returning to the U.S. to delete any truly sensitive information on your phone, tablet, or laptop. The biggest concern: delete any communication or social-media apps on your phone that you don’t want someone looking at. As part of a search, CBP agents could easily open your mail or Facebook app and scan messages, friends, and recent activity. (Cope says EFF has heard, anecdotally, of this happening already.)
The one thing you can’t do: lie to a CBP agent. CBP officers are federal agents, the same as FBI officers, and deceiving them can result in a charge of “making false statements,” a federal crime that can result in jail time.
The future
Since 2009, when the CBP first established its policies on what it can do when searching your electronic devices, there have been a few major cases that have altered the legal landscape. The first, U.S. v. Cotterman, was a Ninth Court decision that declared that border agents must have “reasonable suspicion” in order to perform forensic examination of your devices. The second, Riley v. California, was a Supreme Court case that determined that when someone is arrested, law-enforcement officials must still provide probable cause and obtain a search warrant before searching their phone. The Electronic Frontier Foundation hopes that the CBP can be persuaded to take both rulings into account when (and if) it considers a new policy, calling the 2009 policy “woefully out of date.”
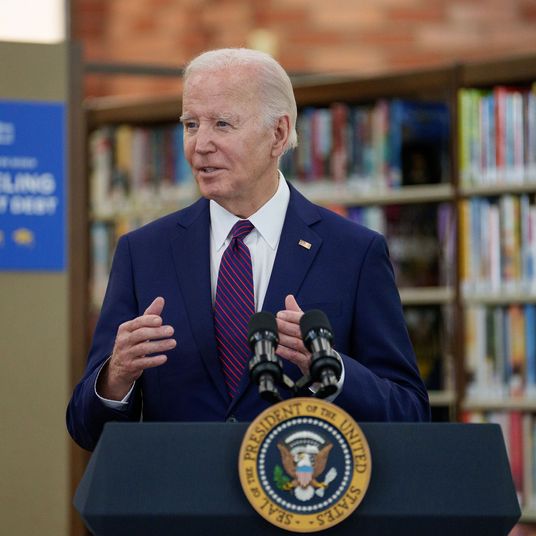
The new Department of Homeland Security chief, John Kelly, makes that seem unlikely in the near term. He’s also declared he wants the CBP to have the right to not only search phones but to also force foreign nationals to provide the passwords to online accounts. “We want to get on their social media, with passwords: What do you do, what do you say?” said Kelly in front of the House Committee on Homeland Security earlier this month. “If they don’t want to cooperate then you don’t come in.”
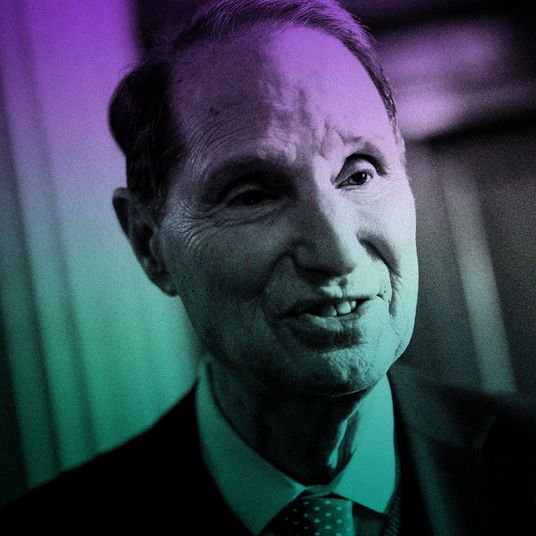
Meanwhile, Senator Ron Wyden, a Democrat representing Oregon, sent a letter on Tuesday announcing that he plans to put forward legislation requiring a probable-cause warrant before a CBP agent could search a phone, or force foreign visitors to give up their online passwords. The bill would face strong headwinds — it would need to make it through Republican-controlled Congress and past Trump’s desk without getting vetoed. Still, it represents the first time that a senator is agitating for a change of the CBP’s policy on searching electronic devices.
The CBP says it prohibits “consideration of race or ethnicity in law enforcement, investigation, and screening activities, in all but the most exceptional circumstances.” But reading through the numerous reports of American citizens who have had their electronic devices searched, it’s hard not to see a pattern: many are Muslim — or might scan as Muslim to a CBP agent standing duty in, say, Niagara Falls. Add to this the continuing turmoil of Trump’s executive orders on immigration from majority-Muslim countries — as they work their way through the legal system (while Trump continues to issue new ones) — and you have a situation that should give pause to anyone who cares about privacy.
The CBP maintains that such searches are rare. “Despite an increase in electronic-media searches during the last fiscal year, it remains that CBP examines the electronic devices of less than one-hundredth of one percent of travelers arriving to the United States,” says a spokesperson to Select All. Per the CBP, from October 1, 2015, to September 30, 2016, 390 million people passed through the border. Of those, 23,877 had their digital devices searched.
Sophia Cope at the Electronic Frontier Foundation remains skeptical. “While the percentage of data searches might be small,” she says, “to the extent that CBP is searching digital devices without a warrant or individualized suspicion, even one constitutional violation is concerning.”
But what can you do while CBP policy stands as is? “The most basic advice we give people is minimize the amount of data you carry with you,” says Cope. “Protect the data you do carry with you through encryption, disengage biometric unlocks, and when you travel, power down your device and use strong passwords.”